IT Infrastructure for small Businesses
Cost effective IT Infrastructure that won’t break the bank
A strong, scalable IT infrastructure is an absolute ‘must have’ for every business, but it doesn’t have to be complicated or expensive. Whether you’re running a busy office, a growing multi-site organisation or supporting hybrid and remote teams, your network, cabling, Wi-Fi, servers and security all need to work together seamlessly so your people can simply get on with their jobs.
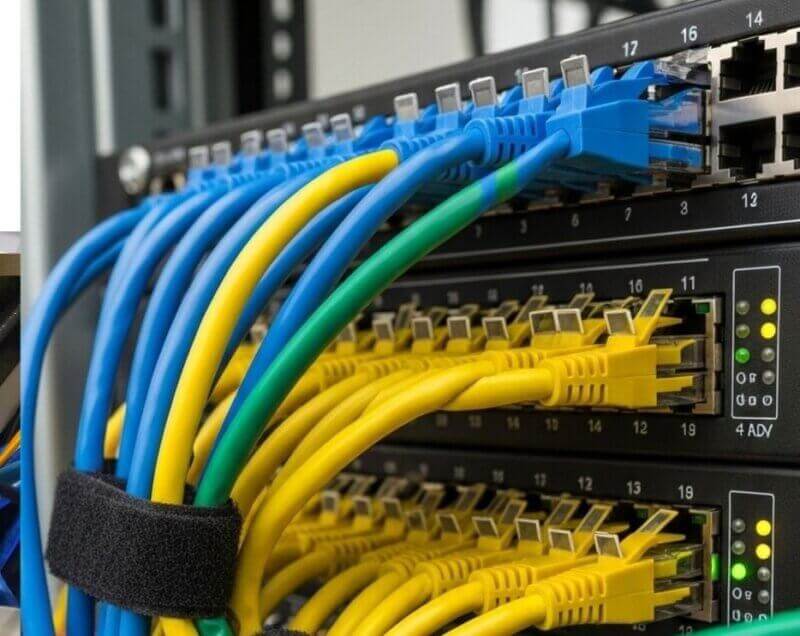
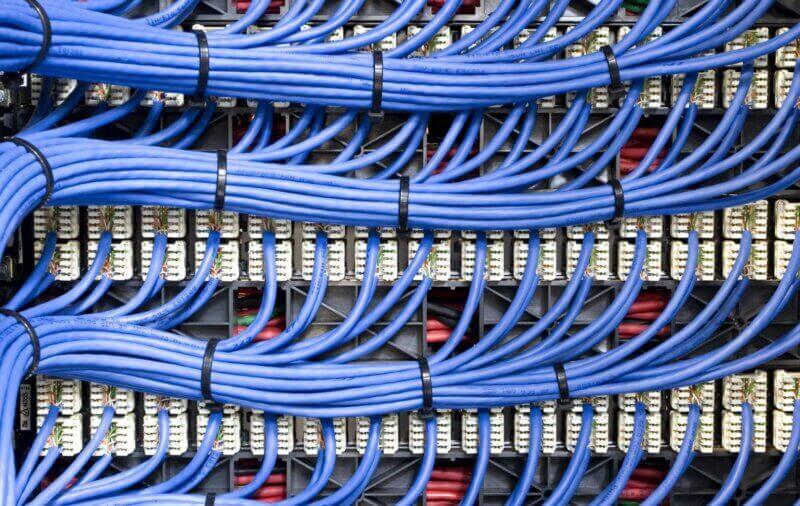
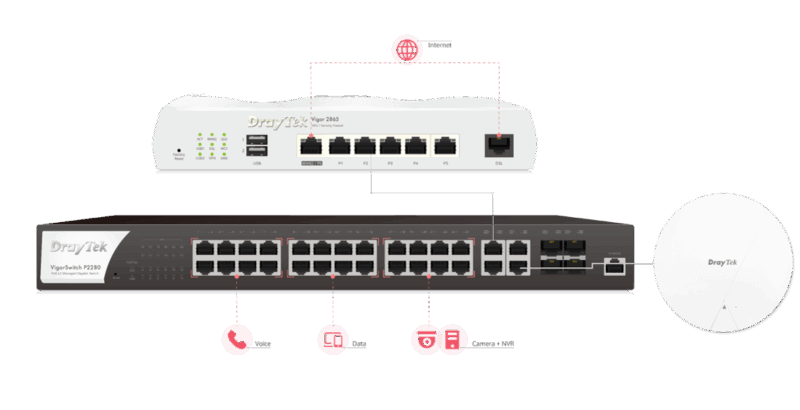
At IT Support UK, we design, install and maintain business IT infrastructure built specifically for small and medium-sized organisations. From tidy, well-planned data cabinets and structured cabling, through to resilient internet connectivity, firewalls, Wi-Fi and endpoint devices, we make sure every part of your environment is reliable, secure and ready for the future. Our team combines enterprise-grade expertise with a friendly, practical approach, no jargon, no drama, just clear advice and neatly delivered solutions.
Good infrastructure isn’t just about technology; it’s about reducing downtime, protecting your data and giving your team fast, consistent access to the tools they rely on every day. With the right foundations in place, you can adopt cloud services with confidence, support flexible working and scale your business without worrying that your systems will hold you back. We’ll help you understand what you already have, where the gaps are and how to move forward in a sensible, cost-effective way, whether that means a small upgrade or a complete refresh.
If you’re planning a new office, struggling with slow or unreliable systems, or simply want reassurance that your existing setup is fit for purpose, we’re here to help. Explore the key building blocks of business IT infrastructure below to see how everything fits together, or get in touch to arrange a no-obligation chat about your network and systems.